Alternatives to the Tor Browser

Content
Tor has long been considered the foundational tool for anonymity on the internet. But today its capabilities are no longer sufficient: the network operates slowly and frequently triggers suspicion on websites.
For stable, private online work, a different approach is needed: fast proxies, correct substitution of the browser fingerprint, and separation of data between sessions.
In this article, we analyze which tools are currently used instead of Tor and how they differ.
Why the Tor Browser Is No Longer a Universal Solution
Tor is a network of proxy servers in which the connection passes through several nodes located in different countries around the world. This scheme hides the user's IP address and complicates route tracking: each node sees only part of the chain, so the full picture cannot be obtained at a single point.
This approach was long considered a reliable method for maintaining anonymity online. However, the level of privacy depends not only on the IP address but also on the browser fingerprint, user behavior, background network activity, and other factors. Tor hides the IP address, but this is insufficient. Modern websites actively use JavaScript, WebAssembly, and other technologies through which data about the device and behavior can be collected and used to identify the user.
For maximum protection in Tor, one must enable the Safest mode and effectively disable the majority of scripts. After this, many websites operate with limitations or stop loading altogether. Under regular settings, some data can still be collected via scripts, reducing the level of anonymity.
Blocks and Access Restrictions.
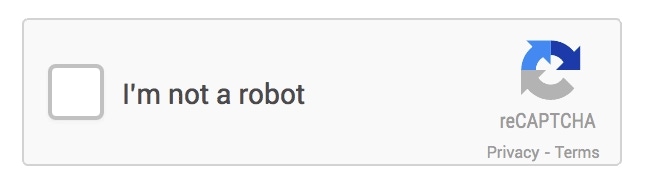
The IP addresses of Tor exit nodes have long been known. A single address can be used by a large number of users, so website protection systems frequently flag such traffic as suspicious.
Consequently, the risks of encountering CAPTCHA, access restrictions, and complete page blocking increase. These issues arise on both high-security services and ordinary websites.
2. Network-Level Risks.
Any participant in the network can launch a Tor exit node. If a site operates over HTTP rather than HTTPS, the owner of that node can view the data as it exits the network.
There is another risk: traffic analysis based on timing. This method compares the moment data enters the Tor network with the time it exits. This is sometimes sufficient to link a specific session to a user with a certain degree of probability.
3. Tor Is Easily Detected.
Using Tor is noticeable at the provider level and by DPI (Deep Packet Inspection) systems that analyze network traffic. The very fact of connecting to Tor can be recorded as a distinct type of activity.
In several countries, this is already sufficient for the connection to fall under additional control or more careful analysis.
Why Tracking Has Long Ceased to Be About IP Alone
The main mistake is assuming that changing the IP automatically resolves the privacy issue. In practice, websites, advertising platforms, and protection systems use dozens of signals simultaneously. The IP is only one of them. Even after changing the address, a user can be identified by their browser fingerprint, device parameters, behavior on the site, and methods of storing identifiers in the system.
Browser Fingerprint. The browser and the device on which it runs have a set of parameters that allow the user to be distinguished from others. Collectively, such data forms a digital fingerprint.
Canvas identification works through hidden graphics rendering in the browser. Due to differences in hardware, drivers, and the operating system, the result varies slightly on each device.
WebGL and AudioContext provide even more technical data. Through them, additional information about the video card and audio processing can be obtained.
Data is also collected on fonts, the number of processor cores, memory volume, screen resolution, and other device characteristics. All of this is used as part of the fingerprint.
Behavioral Biometrics. Websites can analyze user behavior: mouse movement speed, cursor trajectory, typing rhythm, pauses between keystrokes, and scrolling patterns. Based on this data, users can be distinguished from one another even if their devices' technical parameters match.
Tracker Masking and Identifier Storage. Trackers disguised as elements of the site itself — such as its subdomains — are used for tracking. Because of this, the browser and blockers perceive such requests as internal, while data collection about the user continues through them.
Cookies, Local Storage, IndexedDB, and other browser mechanisms are used for storing identifiers. After deleting cookies, some of this data may persist or be restored, allowing tracking to continue.
What Alternatives to the Tor Browser Exist?
The choice of alternative depends on the task. For ordinary surfing, certain solutions are suitable; for accessing hidden services — others; for strict environment isolation — yet others.
VPNs and Privacy-Focused Browsers
One of the most common options is using a VPN in combination with a browser featuring enhanced privacy protection. This setup helps hide the IP address, reduce the volume of collected data, and limit tracking opportunities.
Such solutions generally share a common principle: limiting telemetry, protection from trackers, stricter privacy settings, and reducing the number of signals by which a user can be recognized. However, the level of convenience, data isolation, and resistance to modern tracking methods varies among different tools.
Decentralized Anonymous Networks
Besides Tor, there are other anonymous networks, such as I2P. They are used to access services operating within their own closed environment rather than on the regular internet.
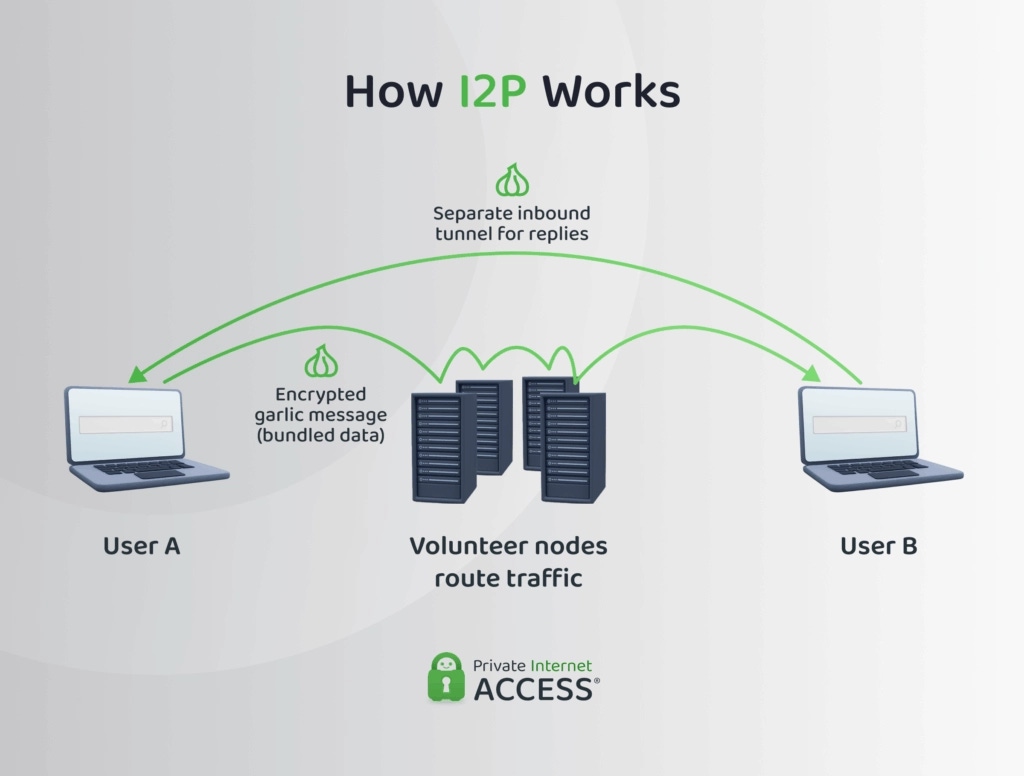
Such networks are relevant in environments where services initially operate within their own anonymous infrastructure. They are less suitable for ordinary websites, as access is more complex to configure.
Antidetect Browsers
Linken Sphere, Dolphin Anty, Multilogin, AdsPower, and other antidetect browsers were created for marketing, traffic arbitrage, and multi-accounting. Their purpose is to form separate browser profiles with different parameters that appear plausible to website protection systems.
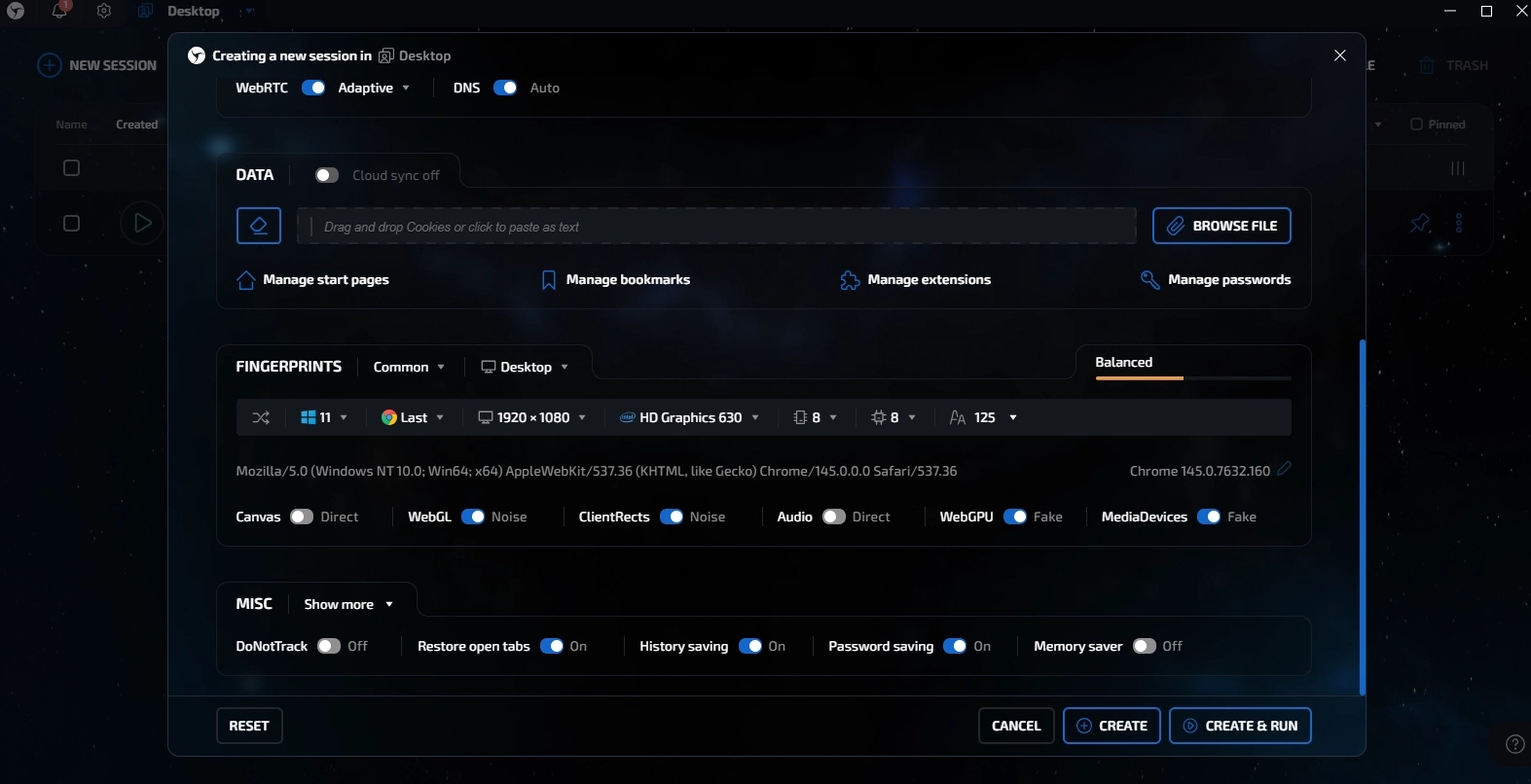
Through this approach, accounts and actions are not mixed in a single environment. Each profile has its own settings, cookies, sessions, and technical parameters, reducing the risk of linking different scenarios together.
However, most popular antidetect solutions are specialized software for the professional market (traffic arbitrage, crypto farms, and team operations). For an ordinary user, their functionality is often excessive, and the cost unjustifiably high. You are essentially overpaying for automation tools and team access features that are unnecessary for simple privacy protection.
Isolated Operating Systems
When risks are elevated, a single browser is no longer sufficient. In such cases, systems like Qubes OS are used, where different tasks are launched in isolated environments.
This separation prevents different processes from mixing within one system. If one environment proves vulnerable, it does not automatically grant access to all other data and tasks.
Noid as a More Convenient Alternative to Tor
For everyday surfing, users often choose alternatives to Tor that do not require complex setup and do not create constant problems when interacting with websites. One such option is Noid. This browser is suitable for private surfing and working with different accounts within the same service.
Simple Setup and Quick Start. In Noid, the profile is created automatically, browser parameters are selected by the system, and data is stored locally on the device. The browser does not require lengthy manual configuration before use.
Separate Profiles for Different Tasks. Because of this, accounts, browsing history, and user actions are not mixed within a single environment.
Local Data Storage. Profiles and user data are saved on the device. This approach reduces risks associated with external access, leaks, and storing all information in a single cloud environment.
Built-in Ad Blocker. It removes intrusive advertising elements, reduces the number of trackers on sites, and decreases the number of unnecessary requests during surfing. As a result, pages load more cleanly, and the user leaves fewer data traces during ordinary site browsing.
Noid is suitable for everyday surfing when privacy is needed without complex manual configuration. The browser can be used for viewing sites, accessing services blocked in your GEO, and working with different accounts without mixing activity within a single profile.
Conclusion
Tor remains one of the most well-known tools for private internet access. At the same time, in modern conditions, hiding the IP address alone is insufficient, as systems track the browser fingerprint, background network activity, and other factors.
Anonymity depends on several factors: browser settings, data storage, profile separation, and protection from excessive information collection. The secure browser Noid takes this into account and implements it without unnecessary complications: it automatically creates a profile, stores data locally, separates different scenarios into distinct profiles, and blocks ads and trackers — making it a convenient tool for everyday use.
FAQ
— Why do websites block Tor?
— The IP addresses of Tor exit nodes have long been known and frequently appear in databases of suspicious traffic. Because of this, sites and protection services may display CAPTCHA, restrict access, or completely block the connection.
— Does ad blocking help increase privacy?
— Yes. A built-in ad blocker reduces the number of advertising scripts, trackers, and background requests from sites. As a result, the user leaves fewer digital traces.
— Is the Tor Browser safe for ordinary use?
— Not entirely. Tor hides the IP address but does not solve all privacy tasks. The very fact of connecting to this network may raise suspicions among protection systems.
— Which browser is suitable for private surfing without complex setup?
— For such tasks, solutions with automatic profile configuration, local data storage, separate profiles, and built-in protection from ads and trackers are usually chosen. Noid covers this everyday use scenario.


