Privacy on the Internet in 2026 and the Capabilities of the Secure Browser Noid

Content
In 2026, it has become obvious that complete privacy on the internet does not exist. Many users still believe that "Incognito" mode in the browser or a regular VPN makes them fully anonymous. In reality, this is a misconception.
Incognito mode only hides browsing history from other users of the device. The internet provider and the websites themselves still see network activity. A VPN encrypts traffic and changes the IP address, but even this is no longer sufficient. Today, websites use far more data to identify users. The browser transmits dozens of parameters — from the system version and installed fonts to device characteristics and browser settings. Therefore, even when the IP is changed, websites can recognize the user. In modern conditions, privacy protection requires a more comprehensive approach than just Incognito mode or a VPN.
In this article, we'll break down what methods websites use to track users, what a browser digital fingerprint is, and how the secure browser Noid helps enhance privacy on the internet.
How Websites Track You on the Internet
Websites collect technical data about the browser and device. Even if one parameter is hidden, the user can be identified by other signs.
1. IP Address and WebRTC Leaks
Changing IP via VPN or proxy is only the basic level of protection. The problem is that the browser itself can sometimes reveal the user's real IP address through WebRTC. This technology is needed for video calls and voice chats, for example in Google Meet or Zoom. But through WebRTC, websites can determine the user's real IP address.

2. Cookies and Other Data Storage Methods
Cookies have long been the primary method of tracking users on the internet. With their help, websites save login sessions, settings, and unique visitor identifiers.
Today, cookies are not the only tool. Modern websites also use built-in browser storages, such as LocalStorage and IndexedDB. They allow storing data directly on the user's device. Special identifiers can be written there to help recognize the user between visits. Even if cookies are deleted, some data may remain in these storages until the user completely clears them.
In the past, other mechanisms were also used for tracking. One of them was ETag, associated with page caching. Such methods are now encountered much less frequently.
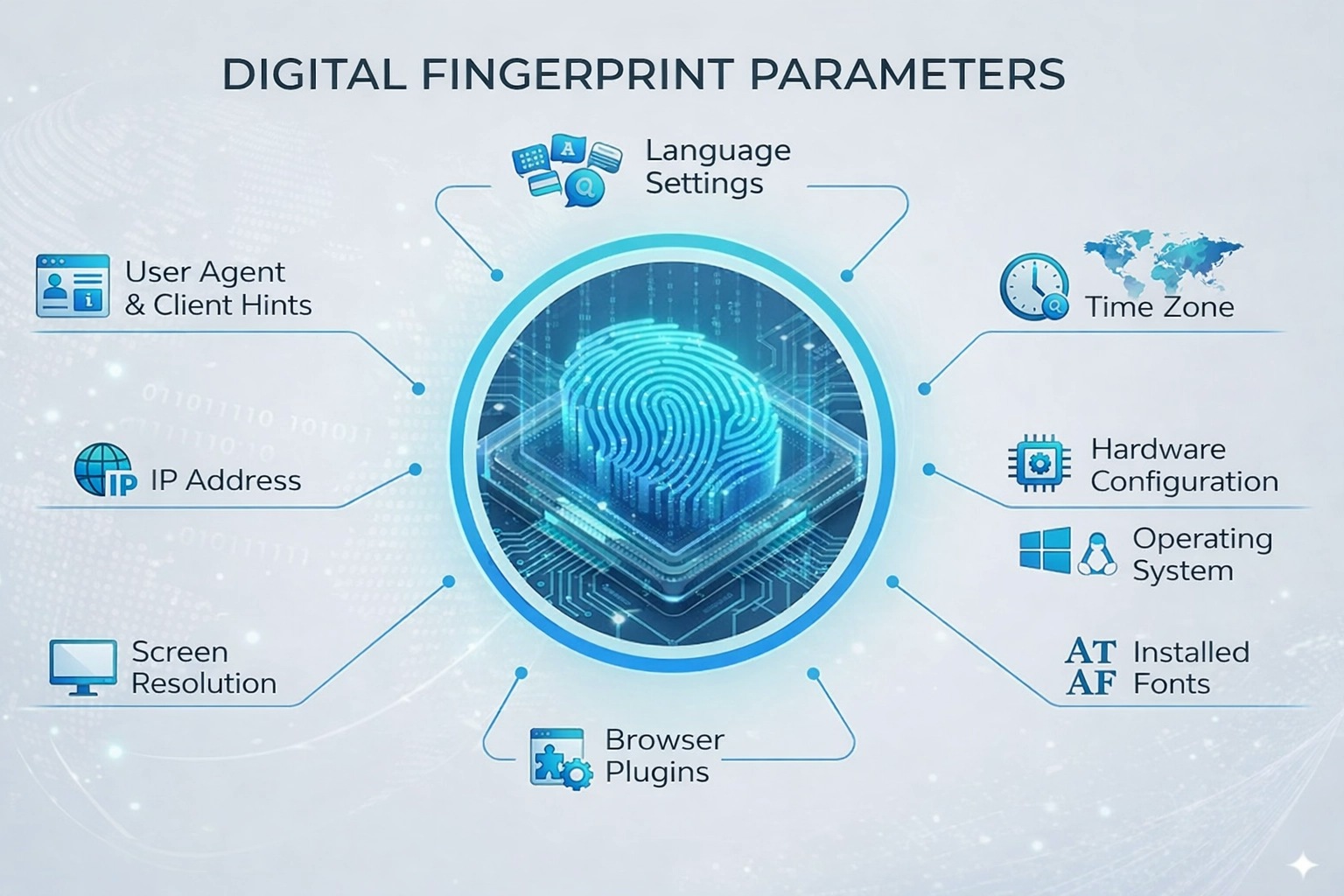
3. Device Digital Fingerprint
The digital fingerprint is formed from numerous technical parameters of the device and browser. Websites use different technologies to collect this data.
Canvas. Canvas technology allows drawing graphics directly in the browser. To check, a page may ask the browser to render an image with text and graphic elements.
Due to differences in the operating system, video card, drivers, and browser settings, the rendering result differs slightly on each device. These differences can be used to form a unique digital fingerprint.
AudioContext. Another method is associated with sound processing in the browser. Using AudioContext, a page can generate a test audio signal and analyze how it is processed by the system.
Small differences in audio driver and hardware operation create unique signal characteristics. This data can also be used as part of the device digital fingerprint.
WebGL. This is a technology for displaying 3D graphics in the browser. Through it, information can be obtained about the graphics processor, drivers, and rendering capabilities.
4. Behavioral Analysis
Websites analyze not only the technical parameters of the device but also the user's behavior on the page.
For example, mouse movement, click speed, page scrolling, and other actions may be considered. This data helps understand how the user interacts with the website.
Sometimes algorithms pay attention to unnatural cursor movements, actions that are too fast, or repetitive behavior scenarios. Such signals can be used as an additional factor when analyzing user activity.
Why Traditional Protection Methods No Longer Work
Understanding that websites actively track users, many try to protect themselves using simple solutions. Most often, these are VPNs, browser extensions, or free proxies. However, in modern conditions, such methods prove insufficient.
There are many extensions that promise to protect the user by substituting the browser digital fingerprint. Such tools include various plugins for changing Canvas and WebGL.
In practice, such solutions rarely work correctly. When an extension intervenes in the browser's operation and adds random "noise" to fingerprint parameters, the result often looks unnatural.
Another common way to bypass restrictions is using public or free proxy servers. However, such solutions have serious drawbacks.
First, free proxies often work slowly and unstably. Second, some of them may transmit additional information about the connection, allowing the user's real data to be determined.
Furthermore, part of public proxies is managed by unknown operators. In some cases, such servers may be used for intercepting unencrypted traffic or collecting user data.
Noid: Privacy Protection Without Complex Settings
Antidetect browsers were originally created for professional tasks and managing large numbers of accounts. Therefore, such tools are often overloaded with settings and have quite high costs.
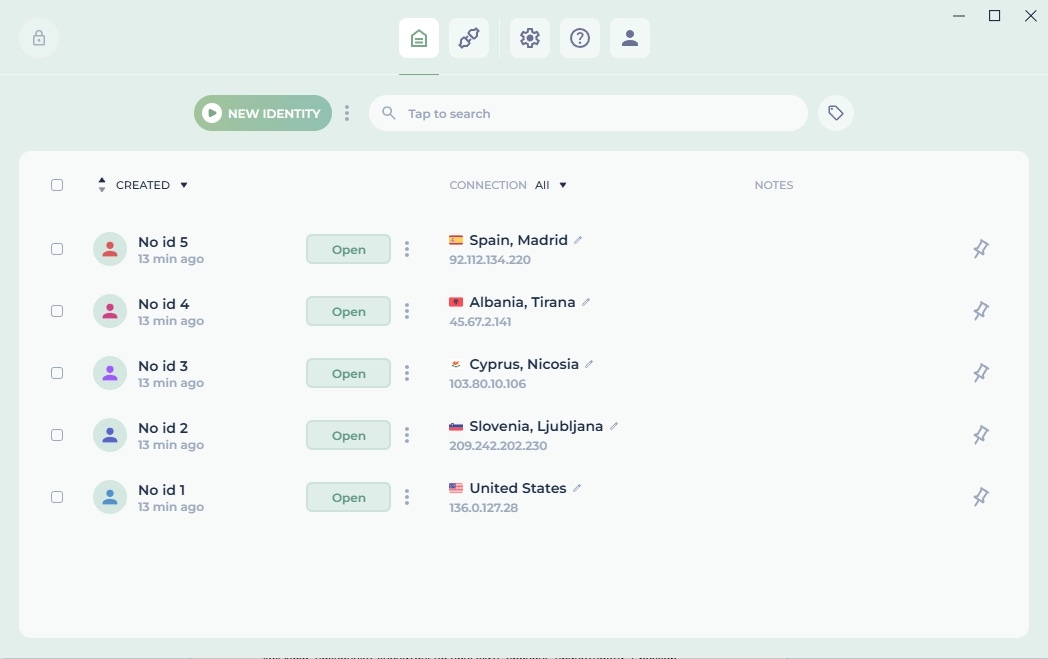
Noid offers a different approach. The browser is oriented toward users for whom it is important to maintain privacy on the internet, use several independent profiles, and bypass regional restrictions without complex technical settings. Most parameters are selected automatically, so the user doesn't need to manually configure dozens of technical profile characteristics.
WebRTC Masking
Many plugins simply disable WebRTC to prevent IP address leaks. However, this may look unusual for some websites, because most users have WebRTC enabled.
In Noid, WebRTC continues to work, but network data is synchronized with the proxy being used. As a result, when checked, the website sees the proxy's IP address, not the user's real address.
Consistent Browser Parameters
Another task of a secure browser is creating a plausible device digital fingerprint.
In Noid, system parameters are selected automatically. If a profile is created on a Windows basis, the browser uses corresponding system fonts, WebGL settings, screen resolution, and a correct User-Agent. Thanks to this, the profile looks more natural and doesn't stand out in terms of basic environmental parameters.
Local Data Storage
All profile data is stored locally on the user's device in encrypted form. They are not transmitted to the cloud or synchronized with the service's servers.
This approach reduces the risk of leaks and allows the user to fully control their data.
Practical Tips for Using Noid
To use the browser and reduce the risk of blocks, it's worth following several simple rules:
Use quality proxies. Noid already has built-in proxies in different locations available, so in most cases, the browser is ready to work without additional settings. If necessary, you can also connect your own proxies.
Check the profile before use. After creating a new profile, it's useful to check it on special services. For example, websites like BrowserLeaks or Pixelscan show what IP is detected, whether there are WebRTC leaks, and what the browser digital fingerprint looks like.
Watch for setting consistency. For example, if the proxy is located in Germany, then the browser language, timezone, and other profile parameters should correspond to that country. Mismatches in such parameters may trigger additional checks from websites.
Conclusion
Modern websites use several methods to track users: IP address, cookies, browser digital fingerprint, and behavioral analysis. Therefore, regular Incognito mode, VPN, or individual extensions no longer provide full protection.
Separate solutions are used to maintain privacy. One option is the Noid browser. In it, the profile is created automatically, parameters are selected by the system, and data is stored locally on the user's device. As a result, the user gets a convenient tool for private web surfing and bypassing regional restrictions without complex setup and unnecessary services.
FAQ
— What is WebRTC and why is it dangerous?
— WebRTC is a technology built into the browser for direct data transfer (audio, video) between users in real time. Its main danger is that it can bypass the classic VPN tunnel and directly address your network card, revealing your real IP address to the website.
— How can you bypass regional restrictions using an anonymous browser?
— In Noid, you can use a proxy from another country. The website will see the IP of the selected location, so access to regionally restricted resources may open up.
— Can an anonymous browser completely protect against tracking?
— Complete anonymity on the internet does not exist. However, tools like Noid allow you to significantly increase the level of privacy. The browser creates isolated profiles, automatically selects environment parameters, and stores all data locally on the user's device. This noticeably complicates tracking activity and linking different sessions together.
— Why does Noid need built-in proxies?
— Built-in proxies allow you to start using the browser faster without separately purchasing and configuring third-party solutions. The user can select a suitable location and immediately proceed to private surfing and accessing needed resources.


