The Difference Between a Secure Browser and a VPN

Content
Many users buy expensive VPN subscriptions for the sake of anonymity. They enable an encrypted tunnel, change their IP address, and think they are now fully protected. Then they open a regular browser — like Google Chrome — and this is where the main problem arises.
Standard browsers transmit numerous technical parameters to websites: device type, screen resolution, system language, font list, and other characteristics. Based on these, a browser fingerprint is formed. Ad networks and analytics systems use it to identify the user even without their real IP address.
As a result, a VPN only hides the IP address and traffic but does not make the user anonymous. If you open a personal email or another account in the same browser, algorithms quickly link the actions and determine the real profile. Therefore, for true privacy, it is important not only to change the IP but also to isolate the environment in which websites are opened.
In this article, we will break down why a VPN alone is insufficient for anonymity, how websites track users through the browser, and what tools help protect your data online.
How a Browser Stores Data: Cookies, Cache, and History
A regular browser constantly saves information about user actions on the device: browsing history, page cache, and cookies. Cookies are small text files that websites use to identify the user and save session data — for example, so you don't have to enter your password every time you log in. LocalStorage works similarly — this local browser storage allows websites to remember settings, visit times, and other interaction parameters.
At the same time, a VPN has no effect on this data. The service only changes the external IP address and traffic route. All local files (cookies, cache, and history records) remain on the device. When opening new pages, the browser automatically transmits this information to websites, which can use it to recognize the user.
How Websites Use This Data
Many websites and ad networks use cross-tracking technologies. They allow analytics systems to track user activity across different web resources and gradually form a unified behavioral profile.
In practice, this works as follows. A user opens Gmail and logs into their Google account. Session identifiers, cookies, and other device parameters are saved in the browser. Then they enable a VPN and navigate to another website. If this site has analytics scripts or ad pixels from major platforms installed, they collect the browser's technical data: IP address, device characteristics, system settings, and other signals.
Even if the IP address has changed due to the VPN, the systems will correlate the data with the existing user profile using browser identifiers, ad cookies, and fingerprinting. As a result, actions on different sites can be linked together.
How a Secure Browser Differs from a VPN
Users often confuse network anonymity with device protection. In reality, these are different technologies that solve different tasks and do not replace each other.
Channel Protection (VPN)
A VPN operates at the network level. It creates an encrypted channel between the user's device and a remote server. The internet provider only sees the fact of connection to the VPN but cannot view the contents of the transmitted data
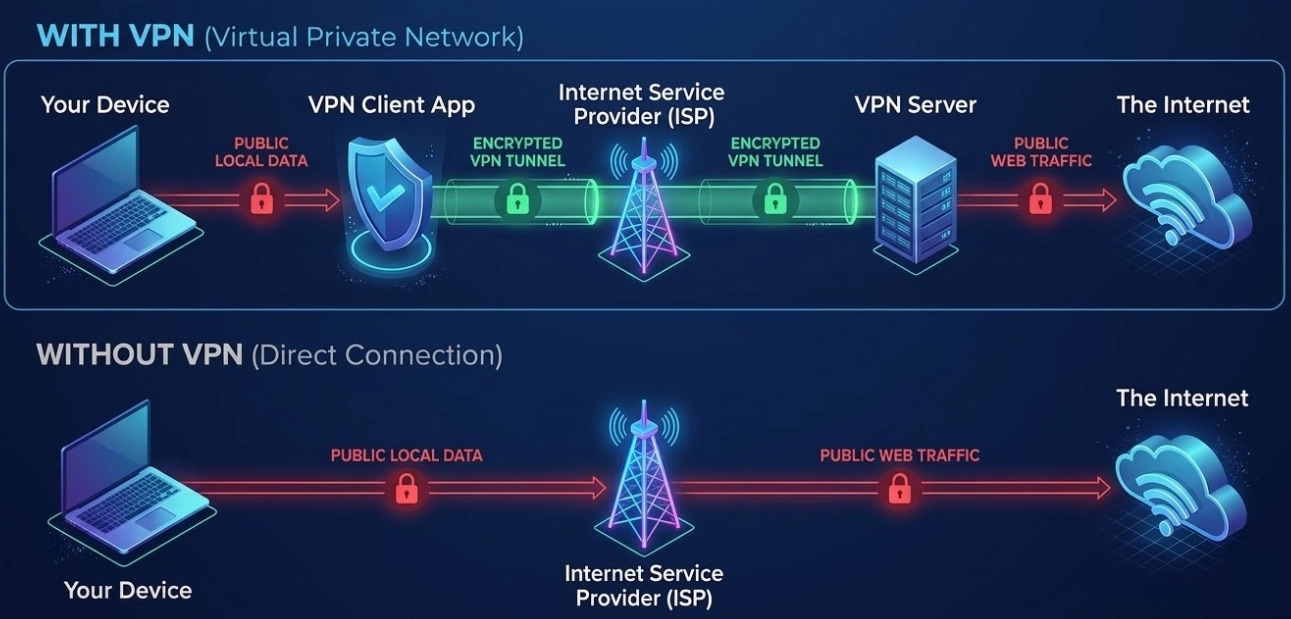
However, the VPN's capabilities effectively end there. The service hides the real IP address and encrypts the traffic route but does not affect the browser's operation. When loading pages, websites continue to receive the device's technical parameters: system language, screen resolution, font list, and other characteristics.
Once the data reaches the website, tracking mechanisms kick in: analytics scripts, ad trackers, and browser fingerprinting technologies.
How a Secure Browser Works
If a VPN protects the data transmission channel, a secure browser operates at the device level itself. Its main task is to isolate different sessions and prevent websites from linking them together.
Such browsers create separate protected profiles. Each profile operates as an independent environment with its own cookies, cache, local storage, and history. Data from one profile does not intersect with data from another.
Furthermore, secure browsers substitute the device's technical parameters. Screen resolution, system language, font list, and other characteristics are selected in such a way as to form a new digital fingerprint for the browser.
As a result, for websites, each profile appears as a separate device rather than the same user.
Practical Applications
Browser profile isolation is used in situations where it is important to separate different online accounts and actions.
Bypassing regional blocks and protection from trackers. Anonymous browsers allow safe visiting of any resources. The user can read blocked sites, visit forums, or leave comments. Ad networks do not track this activity.
A secure browser technically severs the new session from the main account and personal social networks. Tracking algorithms receive a generated digital fingerprint instead of the device's real data.
Secure work with crypto exchanges and marketplaces. If a user manages several stores on marketplaces or controls different crypto wallets, a standard browser links these accounts through cache or system fingerprints. This can lead to a ban for multi-accounting. In a secure browser, each profile is recognized by the platform's algorithms as a separate computer. The risk of automatic banning when working with multiple accounts is eliminated.
Profile isolation technology solves many problems, but there is a difficulty in choosing the tool. Most services on the market are created for professionals. Such tools are expensive, feature complex interfaces, and often store profiles on third-party servers. For an ordinary user, such functionality is often excessive.
Noid Browser: Local Operation Without Cloud Synchronization
Most antidetect browsers were created for arbitrage teams. Therefore, they are expensive and overloaded with features for collaborative work. The interface is complex, and setup requires time and experience.
Moreover, such services often store profiles on third-party servers and require separate proxy purchases. For an ordinary user, this entire system turns out to be too complicated and inconvenient.
The secure and anonymous browser Noid is designed differently. This solution is developed specifically for ordinary users. The tool addresses everyday tasks and provides a maximum level of privacy.
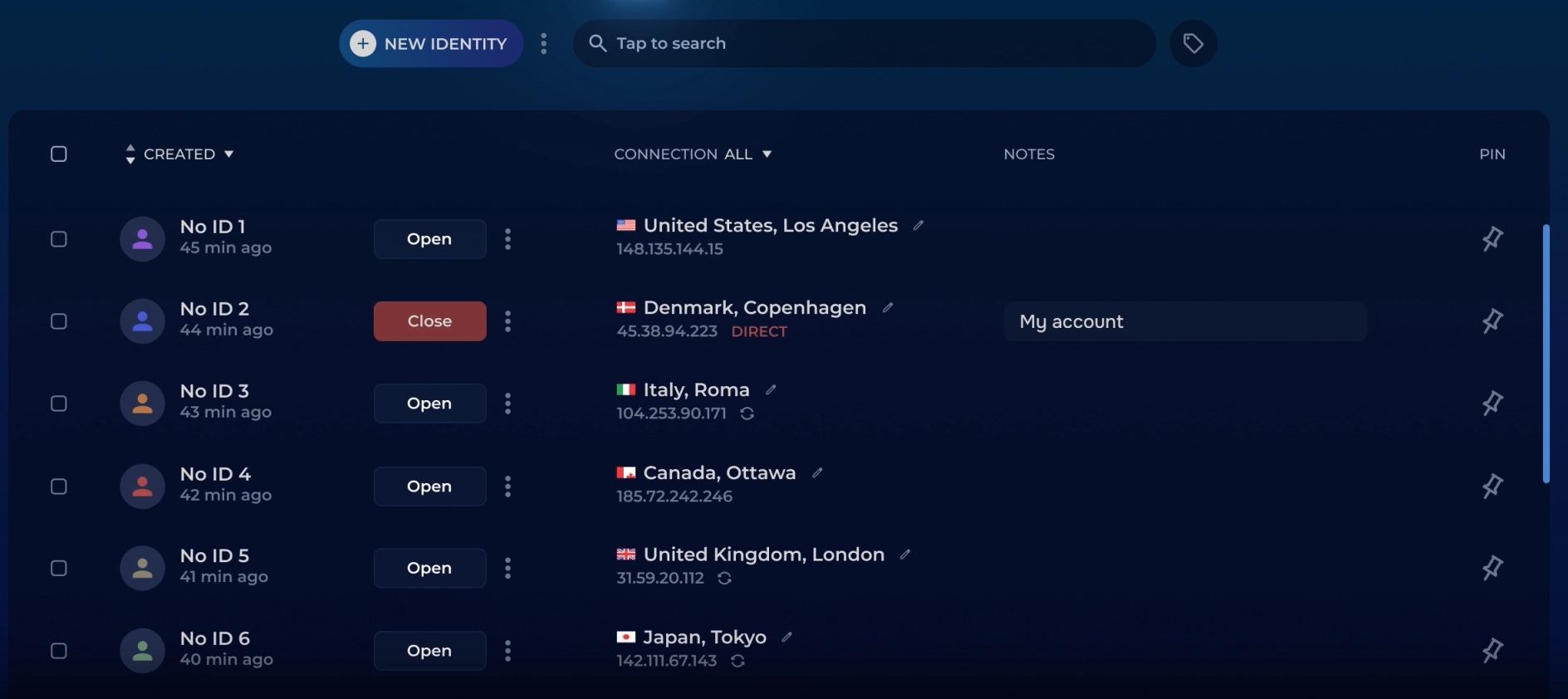
The main difference is that the program does not store profiles in cloud storage. All data, sessions, and system settings remain exclusively locally on your PC's hard drive and are reliably encrypted.
The information is controlled only by the computer owner. For maximum security, Noid can be launched directly from encrypted removable drives — in this case, the program leaves no traces on the computer at all.
The browser already has 14,000 proxies built-in across 50+ locations worldwide, as well as an ad blocker and anti-tracking protection. This is a ready-made solution for securely managing accounts on marketplaces, controlling crypto wallets, OSINT, and bypassing regional restrictions.
Conclusions
Digital privacy today largely depends on what data the browser collects about the user and how websites use that data. In the modern internet, hiding the IP alone is no longer sufficient. Websites collect dozens of the browser's technical parameters and form a user profile based on them. Therefore, real privacy is achieved only when the browser's working environment itself is controlled and sessions are separated.
FAQ
— Why do websites ban me even with a VPN enabled?
— A VPN only changes the user's network address — the IP. However, it does not affect the technical parameters of the browser and device. Modern websites use browser fingerprinting methods: analyzing Canvas, WebGL, font lists, and other system characteristics. Based on this data, a unique digital fingerprint of the device is formed, and websites use it to identify the user even with a changed IP.
— How can I avoid being banned for multi-accounting on marketplaces and crypto exchanges?
— Platforms like Amazon or Binance use anti-fraud algorithms to find linked accounts. They analyze browser data: cookies, local storage, and other technical parameters. If several accounts are opened in the same browser, the platform can determine the connection between them.
You can use secure browsers, for example, Noid. In it, a separate profile is created for each account with its own cookies, cache, history, and system parameters. Therefore, for the platform's algorithms, such sessions appear as logins from different devices, and data does not intersect between accounts.
— Can an anonymous browser be replaced with "Incognito" mode?
— "Incognito" mode is "cosmetic" privacy. It simply doesn't record the history of visited sites on your device but does nothing to prevent websites from recording information about you. An anonymous browser substitutes data at the code level that the browser gives to external trackers.
— How can I check a browser for anonymity?
— You can use independent checking services such as Whoer, Pixelscan, or Iphey. A regular browser with a VPN will show timezone mismatches, WebRTC leaks, or a suspicious fingerprint.


